How to secure your devices?
Our digital devices such as mobiles, laptops, PCs are used for multiple purposes. We install various applications/programs and give access to some of the information on the device while using them. Personal devices contain a lot of private information. Office/Work devices contain confidential information which when leaked may cause damages to the organization including loss of reputation, financial harm, competitive disadvantage, or other forms of harm. Keeping devices secure is important to not give access of your data to malicious attackers or your adversaries.
In this post we will learn how to secure your device.
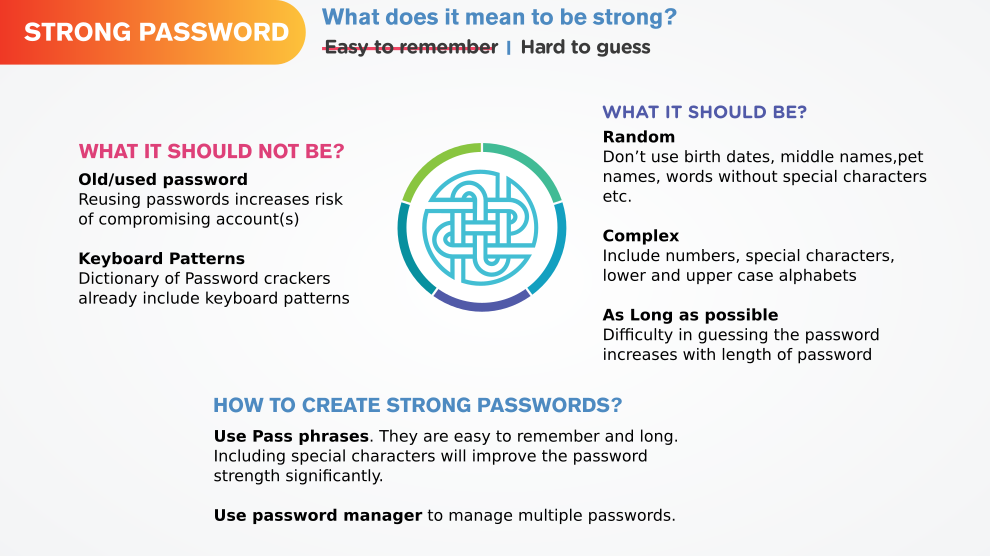
PINs, Root Password, Master Password
Every Device has a built in security lock feature. Setting a password for accessing device goes long way in protecting your information. Choosing a strong password is very important.
Operating System Security
Operating System (OS) is a system software which manages computer hardware resources and provides common service for computer programs for use. Common Operating Systems for Desktops/Laptops and mobile devices are Windows, Linux, Macintosh and Android, iOS respectively.
Security Updates
All the common Operating systems have long term support which means that the organizations/entities responsible for the respective OS will release updates regularly. The updates generally include one or more of bug fixes, security patches/updates and new features. Security updates are very important to ensure that your device does not have the publicly published security vulnerabilities. Malicious attackers can choose security vulnerability to exploit if they have information about your device OS. Common Malware spread on-line are built specifically to work on the old OS and OS which is significantly lagging behind on updates.
It is in your best interest to install the security updates often or automatically.
Security Settings
Depending on your risk profile (read about assessing your risks using threat model from our previous post), it is important to modify the security settings to protect your privacy. Proprietary operating systems such as Windows and Macintosh allow users to create accounts(microsoft account, apple ID) with them and use it to personalize their device. While some features may require you to log in with the respective user account, many do not. You should take some time to understand what information/data you are sharing with the companies and how are they handling it.
Use the privacy/security tips for Windows 7, Windows 10, Mac, Ubuntu and Android published by DuckDuckGo1 to improve your devices' security.
- 1. DuckDuckGo is an Internet privacy company that empowers you to seamlessly take control of your personal information online, without any tradeoffs. https://duckduckgo.com/about
Programs/Applications Security
We install and use many programs/applications on our devices. These software require various permissions for providing the service. While some permissions may be necessary in order to be provided that service, others may be unnecessary. You can choose your software and manage your permissions carefully to ensure that you are not providing more data than necessary for the service that you are being provided.
Install only what you need
By limiting the number of programs/applications you install, you can manage them better. Keeping only necessary software is a good way to do it. Also, device performance degrades with increasing number of software. Many applications on Android run in the background, which may access, monitor and transmit your data and usage patterns data continuously. Reading the privacy policy of the software can help you in making a better decision, but to save time, you could look at the permissions being sought by the application in order to understand what categories of data it might seek access to.
Read our blog post on choosing software which give you complete control.
Mind your Permissions
Software needs permission to access some of your data on the device for providing the service. Earlier, these permissions had to be granted at the time of installing or updating an application. Nowadays, these permissions are generally sought by applications during use. Without necessary permission the service/feature of the application can not work. You might give all the permissions that the application asks for, but this can be very harmful. Applications might ask for more permissions than needed. Think critically about what permissions are being sought by the application and why they require it. If the application does not provide any information regarding why a particular permission is needed or the request does seem reasonable, you should avoid giving the permission. If the application does not work without that permission, avoid using that application and look for alternatives.
Read our blog post on choosing software which have clear privacy policies; ask for only the necessary permissions and also provide details about why they need it.
Common Threats
In the era of Big Data and Digitization, where personal information leak can lead to various harms such as identity theft, loss of reputation, discrimination and harassment, malicious attackers try to acquire the data or access to the computer resources in many ways. Some of the common threats your devices face are in the form of malware.
"Malware is short for malicious software, are programs that are designed to conduct unwanted actions on your device. Computer viruses are malware. So are programs that steal passwords, secretly record you, or delete your data" - Surveillance Self-Defence 1.
Depending on the method and target of attack, the malware is given a special name. Some of these include viruses, worms, trojan horses, ransomware, spyware, adware, scareware, rootkits, keyloggers, screen scrapers etc.
Although there are many kinds of malware, the ways in which a system gets infected are limited and most of them can be prevented by adopting simple practices.
USB/CD/DVD
Using infected drives is the most common way of acquiring malware on a system. Do not use untrusted USBs/CDs/DVDs. It is better to use your own drives and keep autorun switched off in your Operating System for your removable drives.
Malicious Links
For a software to get on to your system it should either be transferred via physical drives or over network. All kinds of malware are out there on Internet, intentionally placed by malicious attackers to trick you into downloading the malware. The URLs of websites/webpages which host the malware are called malicious links. Malicious links can be inserted in Emails, Documents, PDFs, Online Advertisements, Online Content etc.
Pay attention before clicking on a link, if the website or the URL seems suspicious do not click and if you know the person who shared the file or sent the email (depending on where you find the link) ask them about it.
Malicious Files
While browsing Internet, pay caution while navigating through unfamiliar or untrusted websites. Do not download files from unknown sources.
Phishing Attacks
"Phishing is the attempt to obtain sensitive information such as usernames, passwords, and credit card details (and money), often for malicious reasons, by disguising as a trustworthy entity in an electronic communication" 1.
By default, popular browsers like Firefox and Google Chrome will alert you while trying to access a known suspicious website. This is only possible when the website already reported as malicious by others. Phishing attacks can also involve voice calls, SMS or in-person conversations. Pay caution while sharing private information be it via online form, over a customer service call or by any other means.
- 1. Ramzan, Zulfikar (2010). "Phishing attacks and countermeasures". In Stamp, Mark & Stavroulakis, Peter. Handbook of Information and Communication Security. Springer. ISBN 978-3-642-04117-4